Many people are cutting the cord with their cable companies in favor of streaming services such as Netflix and Hulu. Catch up on your favorite show’s current season, past seasons, hit movies, local news, sports and more with one of the following:
$15/month (2 devices)
The ultimate cable TV alternative
•HD, UHD, 4K Channels
•USA CA UK Sports and More
•10+ 4K Channels
•8500+ Premium Channels
•14,000+ VOD
•1,600+ Series
•3100+ 24/7
•NBA, NHL, NFL, MLB
•PPV Channels
•Full EPG Support
•Smart Load Balancing
•3 Days Money-back
•99.95% Uptime
•Firestick • Smart TV • Android/iOS Devices • Windows/Mac Apps • MAG Devices
Free or $5/month for ad-free
America’s only free, nonprofit local broadcast TV digital translator streaming service that provides local broadcast TV channels via the Internet
Starting at $4.99/month
Live sports; breaking news; a mountain of entertainment
$4.99/month after 1-week free trial
•Tens of thousands of episodes & movies
•NFL on CBS live
•Top soccer like Champions League live
•Limited ads
•24/7 national news
Premium: $9.99/month after 1-week free trial
•Tens of thousands of episodes & movies
•NFL on CBS live
•Top soccer plus even MORE live sports
•No ads except live TV & a few shows
•24/7 local & national news
•Your local CBS station live
•Download your shows to watch later
Starting at $64.99/month
Live sports and TV without cable
•100+ live channels
•Clouds DVR
•Family Share
$35/month
The best of cable - all your favorites including news, live sports and entertainment
•No contract
•Free 50-Hour DVR
Starting at $5.99/month
Watch thousands of TV shows and movies
$5.99/month (first month free)
Watch full seasons of exclusive series, current episodes, classic favorites, Hulu Originals, hit movies, kids shows and tons more with limited ad interruptions.
$11.99/month (first month free)
Watch full seasons of exclusive series, current episodes, classic favorites, Hulu Originals, hit movies, kids shows, and tons more with NO ad interruptions.
Hulu+Live TV $64.99/month
•Stream 75+ top Live and On Demand TV channels including sports, news, and entertainment
•Get unlimited access to the largest streaming library (ad-supported). Enjoy full seasons of exclusive series, current episodes, hit movies, Originals, kids shows, and more
•Watch on 2 screens at the same time
•Record Live TV with 50 hours of Cloud DVR storage
•Watch Live TV online and on iOS, Android, Roku, Fire TV & Fire Stick, Apple TV (4th gen), Chromecast, Xbox One & Xbox 360, PlayStation 4, Samsung (select TV models), LG (select TV models), and Nintendo Switch – more devices coming soon
Starting at $8.99/month
Unlimited movies, TV shows and more
•Download your favorite shows with the app and watch them later without an Internet connection
•Watch up to four screens at the same time
•Wide variety of award-winning Netflix Originals, TV shows, movies, documentaries and more
•HD and Ultra HD available
The internet is a valuable tool that can benefit kids in the classroom and beyond. But as parents know, the internet also can be a danger to youngsters.
As hard as parents may try to govern their children’s internet usage, kids’ curiosity often compels them to go online when parents aren’t keeping watch. Parental controls are a great way to protect youngsters while they’re online. Setting up such controls may vary depending on the type of devices kids use, and the following guide can help parents whose children use popular Android, Amazon Fire and iOS devices.
Android
The parental controls on Android devices allow moms and dads to restrict access to various types of content, including television shows and movies, games and apps. The Family Link app, which can be downloaded through the Google Play store, enables parents to track their kids’ online usage and even set up limits on how much time they can spend online each day, as well as monitor the location of the device and when it is on. When using the Family Link app, parents will need to create a separate Google account for their children.
Amazon Fire
Amazon Fire is another popular, user-friendly tablet that many children use. Each Fire device comes with FreeTime built-in. FreeTime bans advertisements and restricts purchases so kids cannot spend mom and dad’s money without permission. In addition, FreeTime allows parents to restrict content, ensuring kids will only be able to see content approved by their parents. Adults also can set up time restrictions to limit the amount of time their kids spend online, and they can even prevent access to certain activities, including video games.
iOS
The iOS is an operating system for mobile devices manufactured by Apple. The Screen Time function on iOS devices allows parents to restrict the use of and downloading of certain apps, including those built-in on iOS devices. Parents can specify which websites their children are allowed to visit, preventing them from visiting sites that kids should not see. Screen Time also allows parents to block purchases made through iTunes, ensuring kids won’t run rampant spending money on music, television shows and music.
Parental controls can help parents monitor their youngsters’ tablet usage and protect them from visiting websites designed for adults.
The latest WiFi routers are faster and more versatile than ever, offering many powerful new features. One important feature makes it possible for the router to send data over two different radio frequencies or “bands:” the 2.4 GHz band and the 5 GHz band. Routers that use both bands are called “dual-band” routers.
To get the most out of your dual-band router, it helps to understand the differences between these two frequencies and how the router uses them both to give you the best possible home WiFi experience.
About the 2.4 GHz frequency
Let’s start with the 2.4 GHz frequency. When the first WiFi routers were released, this was the only frequency they used to send and receive data. One of the advantages of the 2.4 GHz frequency is that it can transmit a strong signal over a fairly large area in your home. It is also good at penetrating solid objects in your home, like walls and floors. Overall, this allows you to maintain a strong WiFi connection as you move further away from your router.
One downside of the 2.4 GHz frequency is that it has become more and more crowded. This is partly because it provides fewer channels than the 5 GHz band. As a result, in addition to interference from other WiFi routers located nearby, your 2.4 GHz WiFi network can experience interference from many common household devices. These include microwave ovens, cordless phones, wireless speakers, Bluetooth devices and baby monitors.
And when your network is experiencing interference from these nearby devices, your speed and overall performance suffer.
Another downside is that the maximum speeds offered by 2.4 GHz networks are typically less than 100 Mbps in practice. If there are multiple users trying to perform certain high-bandwidth activities at the same time—streaming HD video for example—then the 2.4 GHz band will likely not be fast enough.
About the 5 GHz frequency
To provide faster speeds, and limit the impact of interference from other devices, manufacturers added support for the 5 GHz frequency in the latest generation of WiFi routers. With two frequencies (bands) available, these dual-band routers can handle much more traffic. What’s more, the 5 GHz band supports speeds that are four times faster than the 2.4 GHz frequency, so devices and applications that use the most bandwidth generally perform better on the 5 GHz frequency. The 5 GHz band also has many more channels than the 2.4 GHz band which reduces interference from other devices.
Like the 2.4 GHz frequency, the 5 GHz frequency has some drawbacks.
In general, it can’t broadcast its Wi-Fi signal as far as the 2.4 GHz frequency, and it is not as good at penetrating the walls and floors within your home.
How do dual-band routers work?
Dual-band routers support both the 2.4 GHz and the 5 GHz frequencies. In most cases, the device you are using to connect to WiFi, such as your laptop or smart phone, chooses the band. For example, your brand new phone might stay on the 2.4 GHz band as long as it can connect to it, even though there may be less congestion and more bandwidth available on the 5 GHz band. It will only switch to the 5 GHz band if you tell it to or if it can no longer connect to the 2.4 GHz band.
Some routers don’t leave the choice up to your devices. They monitor how much traffic there is on the 2.4 GHz band and, if it’s too congested, will steer your devices to the less traveled 5 GHz band. This is referred to as ‘band steering’. Of course, if you still have old devices that can only connect on the 2.4 GHz frequency, these dual-band routers will not attempt to switch them to the 5 GHz frequency.
For many smartphone users, their smartphones are never too far out of reach. It is a reflection of the role these devices now play in everyday life as well as the amount of sensitive information contained within them.
The treasure trove of personal information, including banking info, personal emails and private photos, that smartphones contain makes them tempting targets for skilled cyber criminals. Though phones come with built-in security features, savvy smartphone users recognize the importance of going beyond such features to protect their devices from hackers.
• Update your operating system. It can be a nuisance to update a phone’s operating system. In fact, many smartphone users have regretted an OS update, feeling the updates changed the look and performance of apps they had grown accustomed to. However, updated operating systems are offered for various reasons, one of which is to guard against glitches or bugs in old operating systems that might have made phones more vulnerable to hackers. When prompted to update a smartphone’s operating system, do so right away.
• Avoid public WiFi. Hackers target victims in many ways, including through public WiFi hotspots. Smartphone users who don’t have unlimited data plans may be tempted to use public WiFi when out and about. But doing so makes users vulnerable to skilled hackers who are just waiting to access unknowing users’ personal information, including their financial data. When leaving the house, turn off the WiFi on your phone, only turning it back on when you need it and only if you can access a secure network.
• Accept two-factor authentication. Two-factor authentication was designed so internet users would have another layer of protection against hackers. When attempting to sign into an account, whether it’s email, social media, banking or another login that requires a username and password, you may be asked if you want to enroll in two-factor authentication. This refers to the system in which users receive a temporary code via the messaging apps on their phones that only the users have access to. Some might say two-factor authentication is a nuisance, but receiving and typing in the short code will only take an extra few seconds and it’s a great extra measure of protection against hackers.
When purchasing and downloading apps, only use official app stores such as the Apple Store or Google Play. Some hackers access phones via apps they offer through websites that, on the surface, seem legitimate. However, such apps contain viruses and malware that make it easy for hackers to access phones once they’ve been installed.
Smartphone users must recognize the importance of protecting their phones, and all the sensitive information their phones contain, from hackers.
What’s the difference between the Internet & Wi-Fi?
The Internet is connected networks all over the world. Wi-Fi is your personal wireless network within your home.
Why is a speed test not showing the speed I pay for?
There is a box (usually some type of modem) that brings Internet into your home from your service provider. To get the most accurate speed test, plug your computer directly into an available port on the modem with an ethernet cord before running the test. Use speedtest.net and connect to the Ciello, Inc. server to run your speed test. If you subscribe to a speed package greater than 100 Mbps, we highly recommend that you download the speedtest.net app and run your speed tests from this application. One thing to note: older devices that do not use the newer 5Ghz Wi-Fi frequency may not support speeds greater than 25 Mbps. This is not referring to the new 5G cell phone technology. This is referring to the frequencies that your device uses to communicate with your modem/router in your home.
How can I get the speed I pay for over my wireless device?
The best way is to have a router or gateway that supports the speed you pay for, then make sure:
• the device you are using is capable of the subscribed speed (you may call Ciello to verify that your router is a current model),
• you do not have any viruses or malware running on your device,
• you close down all other applications before running the speed test, and
• you have full bars on your signal before running the test.
All of these things may cause slower speed tests results over Wi-Fi.
Why can’t I get a good signal in certain areas in my home?
The wireless radios in your router/gateway push service out from the device. Think about it like a speaker, the further you get away, the softer the sound is. Your Wi-Fi works the same way. The further away you get, the weaker the signal. If there are things like metal, concrete, thick walls and mirrors, between you and the router these can weaken the signal even more.
The placement of your router or gateway determines where the Wi-Fi signals are strongest in your home or outside your home (such as a patio). The more centrally located, the more of your home it will reach. However, if your router or gateway is in a location where it can’t be moved you can add a mesh unit to regenerate the signal further into other areas of your home. Call Ciello at 852-3538 to discuss adding a mesh unit in your home.
Volunteerism is the life blood of charitable organizations. Many cannot function effectively without volunteers campaigning for their efforts, handling day-to-day activities and serving in many other essential capacities.
During the pandemic, nonprofit organizations have been affected by social distancing recommendations. It’s challenging to lend a helping hand when those hands may inadvertently be passing on a potentially dangerous illness.
Social distancing and other restrictions instituted in response to the global pandemic do not have to stifle volunteer efforts. The internet can be a gateway to volunteer opportunities — many of which can be handled virtually from the safety of home.
Organizations like Goodwill, the United Nations and even AARP offer online volunteering opportunities. Resources such as Volunteer Match also can connect interested parties with organizations that have virtual volunteer options. The following are a few additional ways to become a virtual volunteer.
• Manage social media accounts. Charitable organizations recognize the importance of a social media presence, so prospective volunteers can offer to help nonprofits keep their social media accounts updated and viable.
• Assist those without sight. Volunteers with Be My Eyes can provide important assistance to blind or low-vision individuals. Virtual video calls enable volunteers to communicate with people directly and provide help.
• Offer tutoring or teaching. Virtual learning has become the new norm in many different school districts. Parents who may need assistance with children adapting to remote learning can benefit from quality educators willing to lend their time and skill sets.
• Design and build websites. Organizations may have trouble finding time to keep their websites updated with the latest information. Writers may be needed to keep blogs current, while coders can improve sites and make them more secure.
• Assist call centers. People may have various questions and needs in a time of crisis. Volunteers can be used in retail call centers, online therapy lifelines and even school offices. Remote technology enables calls to be parsed out and answered by volunteers working from home.
• Translate emails and phone calls. Translators are always in demand in an increasingly global society. Bilingual men and women can volunteer as translators so their favorite charitable organizations can effectively overcome any language barriers that may exist between their staffs and the people they’re trying to help.
Staying close to home has become the norm during the pandemic, paving the way for virtual volunteers to make a difference in their communities.
An increased reliance on virtual home instruction has many students rethinking their organizational strategies and daily school schedules. Learning at home is different from being in a traditional classroom environment, but with some effective strategies, students can persevere without missing a beat.
Stick to a schedule
Many students are successful because they follow a schedule. The Center for Social and Emotional Foundations of Early Learning says that routines and schedules are important because they influence a child’s emotional and cognitive development. Children feel secure with schedules, which may help them recognize what’s expected of them.
When learning at home, students should strive to maintain as consistent a schedule as possible, including bedtimes, wake times, hours devoted to learning and time to get outside or engage in downtime activities.
Connect live if possible
There are many free tools and resources available that enable teachers to provide live video lessons or to record them so students can watch them later. Similarly, social networking apps and virtual meeting programs enable students to connect digitally. This can be helpful for collaborative learning assignments or just to see a familiar face.
Stick to tools that work
Once students find apps or systems that work, they should stick with them, offers Khan Academy, an educational tutoring resource. There are many factors outside of one’s control during virtual instruction but maintaining consistency with tools and schedules is one way to feel more confident and secure.
Check student accounts frequently
Just like students, teachers may be learning as they go in regard to remote learning strategies. Students should be sure to check school email accounts or other places where teachers post assignments a few times per day so that they stay on top of all assignments and are aware of due dates.
Reach out to instructors
Allegheny College suggests students contact their teachers if they are unsure of how to participate in remote learning environments. Ask questions about assignments, get clarification on key topics and be sure to tune into any remote chats or virtual “office hours.”
Remote learning is a new experience for many students, and there may be certain struggles or roadblocks. It can be easy to grow frustrated with equipment failures or lack of in-person interaction. Schools employ qualified therapists and guidance counselors who are just a click, call or email away if issues need to be talked through. Students should utilize all resources made available to them. Virtual home instruction can be made even easier with some extra assistance and guidance.
As the COVID-19 pandemic continues, many schools have transitioned from traditional in-person learning to remote learning. This transition poses new and unique challenges to educators as well as students and their parents.
One of the biggest challenges posed by remote learning is keeping students connected to their teachers and their classmates, not all of whom had readily available access to devices that could facilitate such connections. In recognition of that challenge, school systems have worked to procure devices for students only to be confronted by another challenge: low bandwidth.
According to Microsoft, bandwidth refers to the amount of data that can be transferred over an internet connection per second. Low bandwidth can compromise students’ ability to stay connected to their virtual classrooms. In an effort to help students overcome that challenge, Microsoft offers the following tips on how educators, students and parents can manage low bandwidth during remote learning sessions.
• Reduce reliance on video during class sessions. Turning video cameras off during live class sessions can help to overcome the challenges posed by low bandwidth, as live video is a key contributor to excessive use of bandwidth. If video must be used, encourage students to turn off their cameras when they are not speaking.
• Use pre-recorded content. Pre-recording content enables students to stream video over the internet, saving those with low bandwidth the hassle of downloading large video files to their computers. Microsoft recommends educators who pre-record content for their students to stream to instruct those students to use class time to complete assignments. Educators can make themselves available via chat to answer questions students may have about their assignments.
• Avoid video-based assignments. It can be difficult for students with low bandwidth to send very large files, such as videos. Educators can help students avoid that issue by not requiring them to submit videos as part of their assignments.
• Encourage students to sync files to their devices. Each device is different, and each manufacturer has its own instructions on how to sync files to devices. But Microsoft notes that syncing files to a device allows students to read them offline, which is ideal for students with limited internet connectivity.
Low bandwidth poses a challenge for remote learners. Thankfully, there are ways to overcome it so students can keep learning.
Millions of people across the globe volunteer every year. In fact, estimates from the United Nations Volunteers indicate 970 million people volunteered in 2018.
Busy working professionals may wonder how nearly one billion people across the globe find the time to volunteer. One way charitable men and women can pitch in even if they’re pressed for time is to try their hand at virtual volunteering, which makes it possible to lend a hand without leaving home.
Charitable organizations will always need volunteers to pitch in on project sites, but they also need support in other areas. Virtual volunteers can help perform behind-the-scenes tasks that are essential to the survival of charitable organizations.
Nonprofit organizations can benefit greatly from virtual volunteers, who can perform tasks like website design and data entry from the comforts of home on their own time. Virtual volunteers also can help out during fundraising campaigns and strategizing sessions that can help organizations meet their goals. Anyone with a computer and internet access can become a virtual volunteer, regardless of how busy their schedule is. In fact, many working professionals may find it’s easy to fit volunteering into their schedules if they do not have to travel to a project site or the office of a charitable organization.
Virtual volunteering also can make it possible for charitable men and women to help overseas organizations, helping to eliminate the hurdles created by geography and time zones.
Virtual volunteering can benefit volunteers as well as the organizations they help. Jayne Cravens, author of “The Last Virtual Volunteering Guidebook,” spent years studying the benefits of virtual volunteering. Cravens ultimately concluded that virtual volunteering can benefit volunteers in various ways, including allowing them to volunteer with multiple causes and organizations and even affording them more time to volunteer. Cravens also discovered that virtual volunteering makes volunteering possible for disabled men and women or people who live in especially remote areas.
Men and women interested in becoming virtual volunteers should contact a favorite charity to discuss how they can begin lending a hand today.
Staying home dramatically increased reliance on the internet. Heightened use of the internet and digital products puts users at risk when they go online. Brandongaille Small Business & Marketing Advice offers that 82 percent of predators use social networking sites to target victims by learning about them. In addition, many identity theft crimes are perpetrated online.
The following are a handful of ways people can stay safe as they rely on the internet more and more.
• Limit the information you share. Children and adults should limit how much personal information they share online. Do not share bank account numbers, birth dates, addresses, and other information readily — especially on unsecured sites.
• Utilize private browsers. It’s possible to set browsers to private mode and lock down social media accounts to offer the bare minimum of information to the public. However, even with such precautions, websites and applications may be collecting information and using it for marketing purposes. Law enforcement, website administrators and even hackers may be able to access private information, according to the computer security company Norton.
• Take note of your surroundings. People who engage in video chats or share images online should be aware of their immediate surroundings. Do items in the house in view of the camera give indication of personal identity details? Are there any embarrassing or inappropriate belongings in view? Check reflections in windows and mirrors to make sure that others in the house are not inadvertently showing up online as well. Consider limiting video or photo use in bedrooms, especially for children.
• Be careful of attachments. Exercise caution when downloading attachments from unknown sources through social media, chat rooms or email. Do not click on unrecognizable links, which could be harboring viruses that steal data.
• Use only a secure internet connection. Always use a secure internet connection when sharing important data, such as credit card numbers or banking information. Password protect all Wi-Fi networks.
These are some ways to stay safe as internet activity increases in the wake of social distancing mandates.
When you order your home Internet package from your service provider, you usually have several options to choose from. Speed is often the most important factor since a faster Internet connection will improve your overall online experience.
The challenge is that the fastest Internet speeds are typically the most expensive. That’s why it’s important to understand how Internet connection speeds work to ensure you select the right package for the needs of your household.
How is Internet speed measured?
Let’s start with the concept of speed, or bandwidth, as it’s sometimes called. Measured in Megabits per second (Mbps) or Gigabits per second (Gbps), your Internet speed is the amount of data that can be transferred every second over your Internet connection. Your speed determines the type of activities that you can do online and how quickly you can do them.
A connection speed of 1 Mbps, for example, allows you to browse web pages easily, but it’s not fast enough for you to stream HD videos on Netflix. According to Netflix, that requires a minimum connection speed of 5 Mbps. If you tried to stream HD video at 1 Mbps, your video would be poor quality and would likely stutter or pause altogether. On the other hand, a speed of 1 Gbps—one thousand times faster than 1 Mbps—is blazing fast, allowing you to do almost anything, including letting multiple family members stream 4K video simultaneously.
Download versus upload speeds: asymmetrical Internet packages
When you are choosing an Internet package, there are two speeds you need to consider: the download speed and the upload speed.
The download speed is the speed at which data travels from a remote location on the Internet to your Internet-connected device. For example, if you are watching a video on YouTube, the download speed is the rate at which the information in the video stream travels from the YouTube server to your computer or phone.
The upload speed, on the other hand, is the speed at which data travels from your connected device to a remote location on the Internet. For example, if you post a video or a photo onto a social media site like Facebook, the upload speed is the rate at which the information travels from your device to the Facebook server.
With most Internet packages, the download speed is greater than the upload speed. That’s why you’ll sometimes hear people talk about asymmetrical Internet connections, which just means that the download and upload speeds aren’t equal.
Why are download speeds generally faster than upload speeds? Because most online activities—like web surfing, video streaming, and application downloads—involve downloading a lot of data. And for certain activities, like online gaming and video streaming, the faster you can download data, the better.
The upload speed may be important for you, depending on the type of activities you plan to do online. As an example, an amateur photographer that regularly uploads high-resolution photos to a photo sharing site may want to consider ordering a package that offers a faster upload speed. Or, if you work from home, or operate a small business from home, you might also require a faster upload speed.
The bottom line
The bottom line? The speed of your Internet connection has a big impact on the quality of your online experience. So when you’re choosing an Internet package from your provider, make sure both the download and upload speeds are fast enough for the kind of activities you plan to do online.
SLV REC office closed to public
SAN LUIS VALLEY—San Luis Valley REC has been closely monitoring recent events associated with COVID-19 (Corona Virus) in Colorado. Due to the escalating situation, SLV REC will be closing its office to the public March 18 through April 1 for the safety and health of members, employees and the general public.
Members can pay their bills online through SmartHub (slvrec.smarthub.coop), by phone (877-760-7468), at the drop box outside of REC headquarters (3625 US Hwy 160 W in Monte Vista), by mail (PO Box 3625, Monte Vista, CO 81144), as well as at the following local bank branches: First Southwest Banks, Community Banks and Del Norte Bank.
Members can still reach REC for assistance at 719-852-3538 or 800-332-7634 during normal business hours (Monday-Thursday, 7 a.m. to 5 p.m.) or by email at power@slvrec.com.
REC apologizes for any inconvenience this may cause, but rest assured this will not affect the REC’s ability to deliver electricity or Ciello’s broadband services. Crews will remain on-call, and all regularly scheduled maintenance will continue.
In times of social and economic unrest, we often see a rise in malicious activity, including email phishing attempts. The current COVID-19 situation is no exception. Some might see the country’s shift to remote work as an opportunity and, as such, we need to ensure we are acting with caution.
To help identify possible scams, below is a list of recent phishing emails and scams:
• Phishing emails designed to look like they are from the U.S. Centers for Disease Control
• Emails that offer purported medical advice to help protect you against the coronavirus
• Workplace policy changes and announcements
• Emails with official government announcements
• Links to a map of confirmed Coronavirus cases
• Ads and emails requesting help and donations to fraudulent charities or causes
Here are some tips for keeping your home network safe:
• If an email or request seems out of place, please actively verify the identity of the emailer or requester. This validation can be done by directly contacting (do not reply to the communication) the individual using verified methods, such as an email or a phone call to a verified number. Call the individual or company directly on a confirmed or publicly listed phone number.
• Always confirm any financial transaction, whether work-based or personal. Do not click on links in email, rather go directly to known websites for all banking and financial transactions including any donations.
Working from home doesn’t mean you have to feel disconnected from your colleagues. There are lots of tools out there that support the remote worker. Here are just a few:
For video and audio conferencing
• Zoom – Zoom is a top video conferencing app that offers a scalable experience for enterprise users.
• Skype – A powerful, easily accessible collaboration tool for remote employees.
• Google Hangouts – Google Hangout is a great tool for information sharing and communication.
• WebEx – Cisco WebEx is an enterprise solution for video conferencing, online meetings, screen share and webinars.
For document storage, document sharing and overall collaboration
• Microsoft OneDrive – OneDrive is a cloud storage service from Microsoft that allows you to store all your important files securely in one place and then access them virtually anywhere. OneDrive has additional features, as well, like the ability to share and edit documents.
• G Suite – An integrated suite of secure, cloud-native collaboration and productivity apps powered by Google AI. Includes Gmail, Docs, Drive, Calendar, Meet and more.
• Slack – Slack is a messaging app that brings all your communication together in one place. It offers real-time messaging, archiving and search for modern teams.
Enterprise social networking
• Yammer – Yammer is a software tool that enhances internal corporate communication and networks with external partners.
• Workplace by Facebook – Collaboration tool built on the most popular social network.
Many of these tools have free-to-use options, but like most things, you can unlock a breadth and depth of functionalities with the purchase of a package.
New to working remotely? Here are some helpful tips from some seasoned “remote” veterans to help make your teleworking experience more effective and enjoyable.
Communication is key
• Skype, Slack, Google Hangout or email. The more you can communicate your status on projects, the better.
• Consider scheduling weekly or bi-weekly check-ins with folks that you regularly collaborate with, but perhaps you don’t have standing meetings scheduled. Knowing you have that time reserved can be a gamechanger.
• Keep your deadlines on any deliverables up-to-date and show a bit of flexibility.
Routine, organization and environment matter
• Keep your morning routine. Get up, shower, do whatever you would normally do to get ready for your day and use your old commuting time to organize yourself and set your schedule.
• Use noise-canceling headphones.
• Get up, go for a short walk, and talk to someone. You don’t sit for eight hours a day in the office in silence. Find an office buddy and check in with them periodically.
Create boundaries
• When possible, take an actual lunch break, away from your computer.
• Resist the urge to tackle household chores. Or, if you need to finish up a load of laundry, etc., do it on your ‘lunch break.’
• Set work hours and, if possible, a separate physical workspace away from your family room/ kitchen/ main living area. Burn-out is real. It’s hard to turn-off when your computer and office are sitting in sight at all times. If you don’t have a separate office, pack up your computer when the day is done.
Don’t forget meeting etiquette
• Participating in meetings remotely is more difficult than one would think. Be sure to mute your phone when you aren’t addressing the group; shuffling papers by phone speakers, side conversations and colleagues talking on top of each other create a lot of noise and distraction.
• Meeting organizers, please remember the agenda. Organizing participation is essential to a productive meeting, even a loose agenda is better than nothing (or the dreaded round-robin).
Want some additional resources for making an easy transition to telework? Take a look at these LinkedIn Learning options options, courtesy of Touchstone Energy.
The modem/router in your home distributes Internet access to your wireless devices over a set of wireless standards we refer to as Wi-Fi. There are two frequencies that are used to communicate with wireless gear such as your iPad or Amazon Fire TV Stick, as well as a host of other devices.
The two frequencies each have some strengths and weaknesses. The 2.4 GHz frequency has been available for years and provides good coverage in your home or office. It does a good job penetrating walls and other structural objects, thereby providing coverage in multiple rooms as well as covering areas outside of your home. The speeds that this frequency supports are limited but often adequate for web surfing, watching videos and other basic internet usage. The 5 GHz frequency is a newer frequency that has become generally used as well. Its strength is greater speed. However, it does not penetrate walls nearly as well and therefore offers limited coverage in your home. Also, some older devices may not be compatible with the 5 GHz frequency.
Within these two frequencies are channels that can be utilized by devices to establish a wireless communication path within your home— for example, a security system, Wi-Fi extender, older cordless phone and Direct TV/Dish Network devices. Sometimes multiple devices are attempting to use the same frequency and channel, and you may notice something is causing your device to buffer or take a painfully long time to open web pages. We refer to this as interference. Your devices are interfering with each other and are struggling to operate properly.
Enter Self-Healing Wi-Fi from Ciello! We have recently deployed software in our network that can automatically detect these issues and fix them. Your router will select a communication channel for a wireless device that is not experiencing interference and automatically begin communicating with that device over the new channel. This feature will enhance your internet usage experience and ensure that each device in your home is getting the maximum speed possible.
There are times when in spite of picking the best frequency and channel you experience poor speeds, limited coverage or no connection at all in various parts of your home. This is when you need to contact Ciello so our tech support team can optimize your Wi-Fi coverage. In some cases, this may require one of our technicians to come out and add a Wi-Fi Mesh unit in your home to extend wireless coverage to those areas that are getting a poor signal. We offer a mesh unit that works seamlessly with the router in your home so your Wi-Fi coverage is optimal, and you can enjoy all the speed and reliability that our network provides.
Ciello is continually looking for ways to make your internet experience the best it can be! Self-Healing Wi-Fi is just another example of what we do every day to bring you the fastest and most reliable Internet connection possible.

“The cloud” entered the technological lexicon a handful of years ago and has since become a big part of people’s lives. Despite that, many people still do not fully understand the cloud and its capabilities.
When tech companies or apps refer to data being stored or accessed from the cloud, they’re referring to a network of servers that deliver data via the internet rather than from a computer’s hard drive. PC Magazine says the cloud is just a metaphor for the internet.
Thanks to the web, businesses and individuals have more opportunities and greater access than ever before. While some still rely on local storage, which may consist of one hard drive or a local network of a few computers, to keep data or run programs, many others are adapting to cloud computing or cloud services.
Chances are good that you encounter the cloud on a daily basis. Anytime a person accesses or stores information without using a smartphone, tablet or computer’s internal data, he or she is likely storing information on the cloud.
Internet search engines and web-based email programs were some of the first cloud-based computing encounters utilized by the general public. Preparing documents on the internet and saving them for others to access, such as through Google Documents, or using applications like Dropbox to store files, are others. Apple iCloud puts “the cloud” right in its name and helps maintain data and access to apps and files, such as photos, across various Apple devices.
The public is increasingly embracing cloud computing due to a number of benefits. According to the technology resource Recode, an advantage to the cloud is that remote servers handle much of the computing and storage, making it so people and businesses need not necessarily invest in high-end equipment to get the job done. Low-cost alternatives to traditional laptops, cloud-served devices like Google’s Chromebooks make costs lower for consumers and the education market.
The cloud also is an alternative for storage of data-rich files, particularly videos and images. Cloud drives enable people to store and view entire collections of video and photo memories without pushing internal storage to the max or necessitating purchasing mega-drives to handle the files.
Cloud computing can be cost-effective and efficient, but it relies on internet connectivity. That means that productivity can be halted by internet outages or slow service.
Privacy is another possible concern with the cloud. Some people are notably wary about storing sensitive information on the cloud, where hacking or tracking of data may occur.
Another potential pitfall is some cloud services may be one-size-fits-all products that are not customized to fit individuals’ needs. Products or services may be dropped or modified if a cloud company decides to revamp. And support may not be provided for older products.
Cloud computing has become the de facto method of accessing and sharing data. Cloud novices are urged to educate themselves about the services now available. EL186080
Cyberattacks are on the rise. Highly publicized attacks like the one that targeted Colonial Pipeline in May 2021 have sent multibillion dollar businesses into crisis mode, and such attacks affect everyone, including private citizens.
The rise in remote working that resulted due to the COVID-19 pandemic has exposed IT vulnerabilities that put businesses big and small in precarious positions. Ransomware attacks, in which perpetrators seek ransoms after infiltrating and shutting down a network, often target businesses and not individuals. However, cyber criminals can gain access to businesses through their unsuspecting employees, especially when those workers are working remotely. Individuals can take steps to protect their devices from cyberattacks to make their personal and professional information more secure.
According to Ready.gov, a website created by the United States government that’s designed to educate and empower people to prepare for all types of emergencies, including cyberattacks, offers the following tips to individuals looking to protect themselves from cyberattacks.
• Be mindful of what you share online. Limit the personal information you post and share online. Turn off location features and make use of the privacy settings on all your devices.
• Keep software applications and operating systems up to date. Updating apps and your OS ensures your devices have the most current safety features, making you less vulnerable to cyberattacks.
• Prioritize safe passwords. Utilize a password manager and use upper and lowercase letters, numbers and special characters when creating passwords. Two-factor authentication (two methods of verification) should always be used when available.
• Be suspicious when solicited. Be suspicious of anyone or any message that asks you to do something right away, offers something that sounds too good to be true or requires you to enter your personal information. Think before you click, and when in doubt, do not click. Never provide personal information if you’re suspicious or using websites that do not typically require such information.
• Use encrypted (secure) Internet communications.
• Use a secure Internet connection and Wi-Fi network to protect your home and/or business. If a network is lagging, resist the temptation to seek an available yet less secure connection.
• Make accessing your devices as personal as possible. A strong authentication, such as a personal identification number or password that only you would know, can make devices less vulnerable to attacks. Consider using a separate device that can receive a code or requests a biometric scan (e.g., fingerprint scanner or facial recognition) before allowing access.
• Check your account statements and credit reports regularly.
• Only share personal information on secure sites (e.g. “https://”). Do not use sites with invalid certificates. Use a Virtual Private Network, or VPN, which creates a more secure connection. This is especially important for remote workers.
• Employ additional means to block threats. Antivirus solutions, malware and firewalls can block cyberattacks before users even have an opportunity to respond.
• Back up files. Routinely back up your files in an encrypted file or encrypted file storage device so you can access them should you ultimately fall victim to an attack.
• Protect your home network by changing the administrative and Wi-Fi passwords regularly. When configuring your router, use either the instruction manual or speak to your internet-cable provider to set up the Wi-Fi Protected Access 2 (WPA2) Advanced Encryption Standard (AES) setting, which is the strongest encryption option.
Cyberattacks are on the rise, but individuals can take various steps to make themselves less vulnerable.
Getting fast, reliable Wi-Fi in our home networks is essential. We connect more devices than ever to Wi-Fi, including smart phones, tablets, laptops and a growing list of smart devices. And we use them 24/7 for everything from video streaming and social media sharing to home automation and monitoring.
But sometimes it seems like we’re not getting the speeds we should be, such as when it seems to take forever to upload our holiday photos to a photo sharing site, or when Netflix freezes just when we’re getting to the best part of the movie. And while it’s possible that there’s something wrong with your Wi-Fi setup or your Internet connection, there are other factors you should consider first before calling your service provider’s Help Desk.
How much speed do I need?
The first thing to understand about Internet speeds is that certain minimum speeds are needed to enjoy different types of online activities. Video streaming is the best example of this. The better the video quality, the faster your Internet speed needs to be to enjoy it. Streaming companies typically publish minimum speeds for the different levels of video quality: standard definition (SD), high definition (HD) and ultra high-definition/4K.
Netflix provides its customers with these recommendations1:
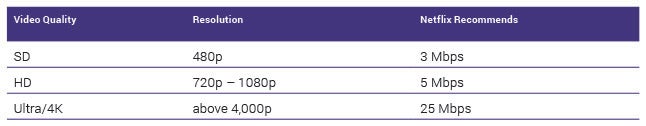
Other streaming companies, such as Hulu, make similar recommendations2. Keep in mind that these are minimum values, which means that even a slightly faster Internet package than the one recommended by your streaming service would likely give you better video performance.
So, before you call your service provider Help Desk to complain that there’s a problem with your Internet service, you need to do two things. First, make sure you’ve purchased an Internet package that’s fast enough to meet your needs for streaming services and when using multiple connected devices at the same time. And second, check to make sure that the device you’re using to connect to the Internet is capable of supporting the speeds being provided by your ISP.
Is your device slowing things down?
The device you’re using to connect to the Internet could be limiting your speed. Apple and Android-based smart phones and tablets have maximum Wi-Fi speeds that they are capable of supporting. If you connect using a smart phone that’s more than three years old, you may not get an accurate picture of the download and upload speeds you’re getting in your home.
There are way too many devices to provide a comprehensive list here, but the first thing you should do is determine which Wi-Fi standard your device supports. If it’s three or more years old, it likely supports the 802.11b, 802.11a/g, or 802.11n standard. If it’s a new device, it likely supports the 802.11ac or 802.11ax (also known as ‘Wi-Fi 6’) standard. The next section provides details on the maximum speed supported by each of these Wi-Fi standards.
Is your router slowing things down?
Another factor that could be slowing down your speed is your router, especially if your router is three or more years old. The Wi-Fi industry is constantly updating its technology to provide users with better performance, so new routers simply work better. They’re faster and provide more reliable connections. Here’s a list of the maximum speed supported by each current Wi-Fi standard, assuming ideal network conditions3:
• 802.11b – 11 Mbps
• 802.11a/g – 54 Mbps
• 802.11n – 150 Mbps
• 802.11ac – 866.7 Mbps
• 802.11ax (Wi-Fi 6) – 2+ Gbps
Note that these speeds represent the maximum speed you can get in theory based on the different Wi-Fi standards. These speeds are not typically achievable in real-world conditions as Wi-Fi signals are affected by obstacles in your home (e.g., large mirrors and concrete walls) as well as other devices in your home that might be transmitting wireless signals (e.g., baby monitors, cordless phones, etc.)
Bottom line: if you’re using an old router, it may not be capable of providing the maximum speed supported by your Internet package. If this is the case, contact your service provider Help Desk and ask them to provide you with the latest Wi-Fi router.
1 Netflix, “Internet Connection Speed Recommendations”
2 Hulu, “Internet Speed Recommendations”
3 Data taken from Juniper Networks, Understanding the IEEE 802.11 Standard for Wireless Networks
Technology advances at such a rapid pace that it can be hard for consumers to keep up. Something that maybe didn’t exist as recently as a few years ago may already be considered obsolete, while some solutions that were on the periphery for years may suddenly become vital to how individuals and businesses operate.
Cloud storage likely qualifies as something that, though it’s been available for many years, figures to become a bigger part of people’s daily lives in the coming years. That likelihood means now is as good a time as any for consumers to familiarize themselves with cloud storage.

What is cloud storage?
According to Amazon Web Services, cloud storage is a computing model that stores data on the internet through a cloud computing provider who manages and operates data storage as a service. Items stored on cloud storage services can be accessed on demand and access is available anytime, anywhere.
How does cloud storage work?
Third party cloud vendors sell and manage storage capacity. So the relationship between cloud storage customer and vendor is not all that dissimilar than the customer-proprietor relationship when renting a physical storage unit to store items people can’t or don’t want to store in their homes. In return for a fee, cloud storage vendors manage data storage infrastructure, including security and durability. But unlike physical storage units, cloud storage customers won’t have to drive to the outskirts of town to access their data like they might if they want to bring that old couch back into their homes. Rather, cloud storage enables convenient, instant access to data. All users need to do is log in.
How does cloud storage benefit businesses?
Cloud storage is convenient for individuals, but its most substantial impact will likely be seen in the business sector. According to AWS, businesses that choose to store their data on the cloud won’t have to purchase any hardware and they’ll be able to add or remove storage capacity on demand.
Is cloud storage secure?
According to SearchStorage.com, a website designed by the B2B marketing services vendor TechTarget, cloud storage security has concerned users since the early days of the technology. However, as cloud storage technology has advanced, so, too, have its security capabilities. For example, AWS notes that all cloud storage data is ideally encrypted, both at rest and in storage. Permissions and access controls should work just as well in the cloud as they do for on premises storage.
More and more individuals and businesses are utilizing cloud storage to house their data. Understanding the technology and how it can benefit users can help calm any concerns people may have about storing files on the cloud.
It’s that time of the year when many areas of the country are under the cold cloak of winter. Unforgiving temperatures can translate into an increase in hours spent indoors, whether at work or at home, and more time relying on devices to pass the hours.

Spending more time watching television, playing video games, texting friends, or browsing the internet can lead to a condition known as “computer vision eye strain.” Eye strain also may be caused through intense eye use, such as while driving long distances or engaging in activities that require close attention, such as crafting or reading.
The American Optometric Association (AOA) says digital eye strain can result in various forms of discomfort, which increase with the amount of screen use. The most common symptoms include:
• headaches;
• blurred vision;
• dry, watery or burning eyes;
• increased sensitivity to light; and
• neck and shoulder pain.
The AOA says viewing a computer or digital screen often makes the eyes have to work harder. The AOA notes this is different from reading a printed page. The letters are not as precise or sharply defined, and areas of contrast can be muted. Also, the presence of glare and reflections on the screen may make viewing difficult. Furthermore, the Mayo Clinic says people tend to blink less while using digital devices and view them at less than ideal distances or angles.
Alleviating eye strain from digital sources involves making changes in daily habits or the environment. Taking regular eye breaks and looking at objects from different distances can help them focus. These tips may help as well.
• Adjust the lighting to reduce glare on screens or your task.
• Limit screen time as much as possible and engage in other activities.
• Consider the use of artificial tears products to lubricate dry eyes.
• Choose the right eyewear, and work with an eye professional to find products that can assist you. Specialized glasses or contact lenses are designed for computer work. Investigate tintings and coatings that also may help.
• Blink often to refresh the eyes.
• Talk to a doctor if eye strain persists or changes in severity.
When the weather gets cold, people may rely on digital devices for recreation more than they otherwise would. Avoiding eye strain in such situations can help people avoid discomfort.

A thriving online presence is important for businesses big and small. While it once was customary to look up a company in a business directory or the Yellow Pages, in the digital era most people look to the internet to find recommendations, reviews and information about businesses. In fact, a strong online reputation can be a company’s biggest asset, while a nonexistent presence can be its most significant liability.
BrightLocal, a marketing firm that connects with local businesses, says 90 percent of consumers used the internet to find a local business in the last year, with 33 percent looking every day. In addition, the average consumer reads 10 reviews before trusting a business. Forbes reports that nearly half of adults in the United States have entered a company’s name into an online search engine before doing business with them.
Locally owned businesses should devote a large share of their operations to establishing and maintaining a positive online presence. Here are some ways to go about it.
• Design a professional website. This should be any company’s first step toward establishing a web presence. Site builders enable business owners to create a website with ease at a relatively low cost. However, for those looking for an extra edge or a customized site, a web designer/coder is a worthwhile investment.
• Commit to social media. Check out what your competitors are doing on social media and then try to mimic some of their actions. Social media requires a strategy, so don’t jump right in. Establish goals and think about how they can complement your business model, lead to brand awareness, customer generation, and more. Social media is fickle and since it is an open-ended platform, customers can communicate with you directly. That can be tricky when navigating both positive and negative feedback. Develop a customer service policy so everyone who is in position to respond to customer input is aware of the best way to do so.
• Optimize how web visitors find your business. Business owners should know about search engine optimization or SEO. According to eTraffic Web Marketing, SEO is the science of directing customers to a company’s website through search engines like Google. Keywords are the building blocks of SEO. These words and phrases are those someone would use when searching that will lead them to your website. Using these keywords in the copy on your website will help customers find your site through searches that much more readily.
• Create high-quality, authoritative content. Use your website and social media accounts to consistently bring new, innovative and informative content to the public. You also can increase your presence in the local community, providing expert advice on topics pertaining to your business and agreeing to be interviewed by local newspapers and bloggers to get your name out there.
American Express suggests keeping on top of customer reviews from various sources (Facebook, Yelp, Google, etc.) and being in constant communication with customers to compete with larger businesses. This can help reduce negative feedback online and boost positive reviews.
Local businesses can increase their online presence to boost their chances of reaching core and new customers.
Cyber Monday is a profitable day for retailers. According to Adobe Analytics, which measured transactions from a majority of popular online retailers in the United States, consumers spent an average of $11 million per minute between 11 p.m. EST and midnight EST on Cyber Monday in 2019. And it wasn’t just the final hour of Cyber Monday that proved popular, as total sales in 2019 increased by roughly 19 percent compared to Cyber Monday a year prior.

The internet has made holiday shopping easier than ever, and retailers capitalize on that convenience every year on Cyber Monday. Savvy consumers recognize there’s great deals to be had on Cyber Monday, but the popular shopping holiday also marks a great time for cyber criminals to target unsuspecting online shoppers.
Holiday shoppers spend more time and money buying gifts online every year, so before the buying season begins it’s wise for shoppers to consider a few strategies for shopping safely this Cyber Monday.
• Beware of malvertising. In recent years, cyber criminals have employed malvertising to trick online shoppers into taking them to websites that look reputable. But looks can be deceiving. Malvertising injects malicious code into legitimate online advertising networks. If consumers accidentally click a malicious ad, the malvertising can trigger a code that installs malware or adware on their computers, redirect users to a malicious website instead of the one the ad suggests or redirect users to a website that looks just like a legitimate retailer’s site, even though it’s not. Update antivirus and ad blockers prior to Cyber Monday. In addition, update browsers and plugins, which can often prevent malvertising attacks.
• Update your software. Skipping or delaying software updates on a computer, tablet or smartphone can make online shoppers vulnerable to hackers and other cyber criminals. Install new operating systems on your devices when such updates become available, and check to see if any new updates can be installed before shopping on Cyber Monday.
• Avoid searching through search engines. When shopping, resist the temptation to look for deals through search engines. Cyber criminals can insert malicious links into search results, directing unsuspecting consumers to malicious websites designed to target their personal information. When looking for deals, visit the websites of established retailers instead of conducting searches through browsers like Google or Firefox.
• Read a URL before buying anything. One old yet still effective trick cyber criminals employ is creating websites that look identical to those of trusted retailers. These copycat sites may only be one letter different from legitimate sites. By reading URLs closely prior to entering any personal information, such as their credit card numbers, consumers can protect themselves from copycat websites.
Cyber Monday is a popular shopping holiday. Cyber Monday shoppers should be as cautious about cyber criminals as they are excited about finding great gifts for their loved ones.
Today’s small business owners face unique challenges that businesspeople of yesteryear never had to confront. While the internet has made it possible for even the smallest businesses to have a global footprint, it’s also forced business owners to devote substantial time to managing their online reputations.
A company’s online reputation can have a major impact on its ability to survive and thrive. The following are a handful of simple ways business owners can manage their companies’ online reputations in the hopes of benefiting their businesses and expanding their customer base.
• Don’t ignore negative reviews. Small Biz Ahead, a service from the insurance provider The Hartford that aims to help business owners manage and grow their businesses, advises business owners to acknowledge negative reviews. Respond privately to customers, apologizing for their unsatisfactory experience and thanking them for their feedback. When communicating with customers, always keep these communications friendly and constructive. Dismissive, confrontational and/or rude interactions with customers will only further damage your online reputation.
• Actively monitor your reputation. Websites such as Yelp and Google, via its Google Reviews capability, give customers plenty of places to go to share their comments about your business. Stay up-to-date on these, making a concerted effort to monitor your reputation. If you’re open for business seven days a week, chances are customers will be reviewing your business seven days a week. Reach out to customers who had negative experiences as soon as possible, and report any comments you feel violate websites’ standards the moment you see them.
• Don’t hesitate to ask customers to edit their reviews. When you successfully reach out to customers who left negative reviews, don’t hesitate to ask them to consider editing their reviews. Many customers are happy to update their reviews if issues were promptly and successfully addressed.
Online reputation management is important for today’s business owners. Though managing online reputations can seem like a full-time job, a positive reputation can greatly benefit your bottom line.
Colorado revised guidelines, forthcoming, April 27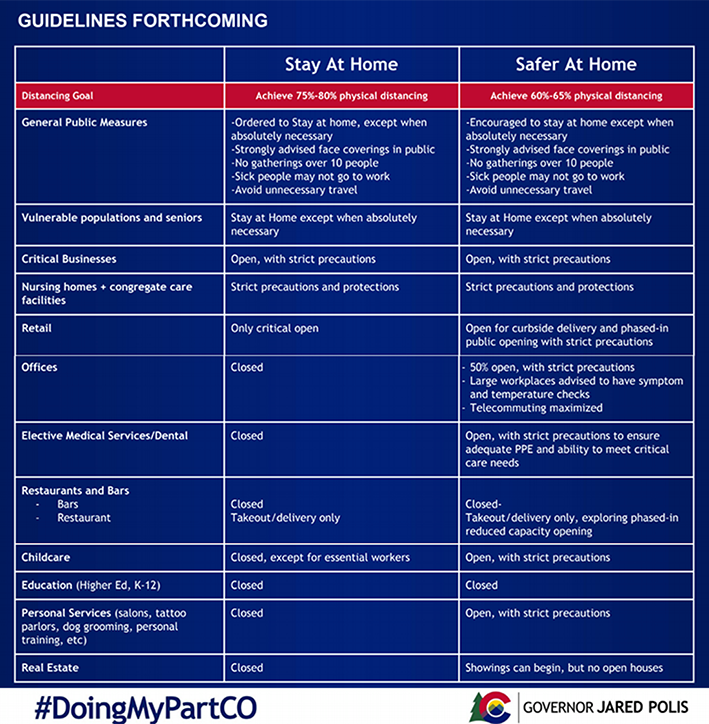

The modern world is driven by technology. People rely on tech for both business and pleasure, rarely letting a day pass without using a device or the internet. But technology is only as effective as its functionality. Failure to clean and maintain tech can compromise its effectiveness.
Cleaning and maintenance may not sound like exciting tasks, but they’re essential for keeping devices running smoothly. Even if one thinks their home or office environment is squeaky clean, dust can accumulate. According to TechRepublic, which empowers decision-makers to identify technologies and strategies to streamline business processes, dust is a fearsome foe in the tech environment. Cleaning dust, among other tasks, is necessary for continued operations.
Physical cleaning
Take time to assess the cleanliness of all hardware and other equipment. Gather supplies for proper cleaning, including canned air, tech-safe cleansing wipes, dusters and a good measure of elbow grease. Target the exterior of the device, cooling vents, ports, the device’s display, keyboard and mouse. All it takes is one small foreign particle to derail components.
DVD and CD-ROM drives (if your computer has them) can be cleaned with special kits and disks.
Don’t forget to inspect outlets and surge protectors. Electric current tends to attract dust bunnies and other debris, which can cause a fire if allowed to accumulate.
Data cleaning
Routinely install updates to keep devices running efficiently and safely. Many updates contain security patches that protect the integrity of your data and maintain the operating system.
The tech resource IT Freedom advises conducting an internal cleaning of any devices. This involves deleting any unnecessary files to free up space, or to remove apps that are not needed. In addition, cut down on the number of tasks running in the background, which can affect speed and efficiency.
If speed is a concern or if the battery is being drained on mobile devices, try turning off Wi-Fi or Bluetooth when it is not being used.
Backups and security
Data breaches have made headlines, and many people have had the displeasure of losing data when a computer or other device fails. Keep personal logins and passwords secret, update virus protection software as needed, don’t transmit vital information over unsecured connections, and routinely back up information to a cloud or external storage device.
Keeping computers, tablets, mobile phones, and other devices clean is essential to ensuring they continue to work effectively.
